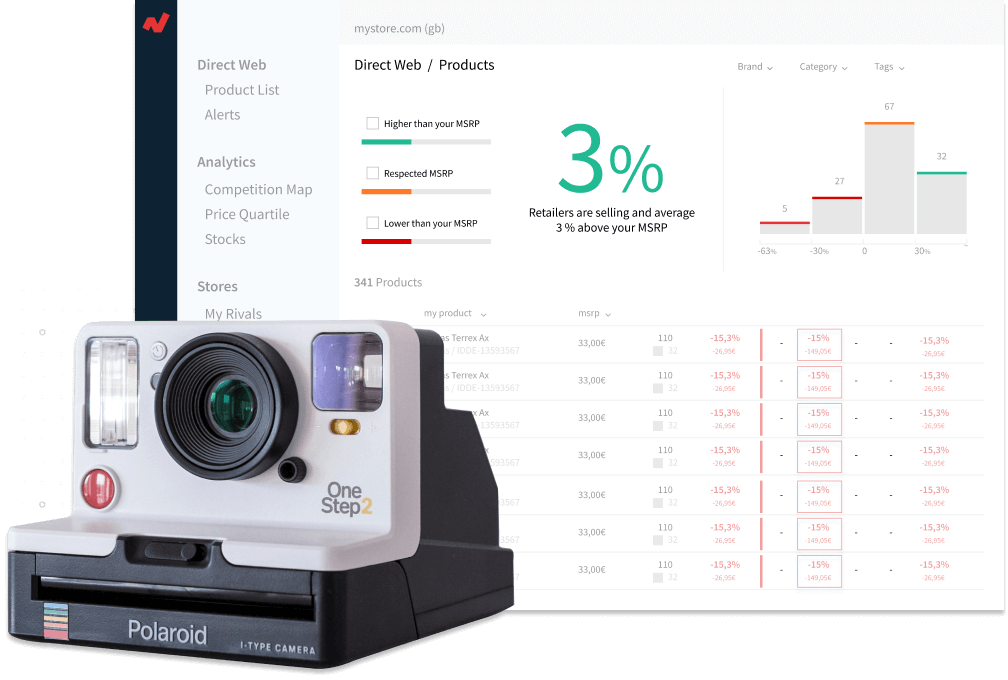
Netrivals is a solution specially designed to meet the needs of pricing departments in e-commerce businesses.
For this reason Netrivals’ security standars are very important.
Netrivals’s primary security focus is to safegaurd our customers’ and users’ data, which is why Netrivals has invested in the proper resources and controls to protect and service our customers. Our investment in security and privacy utilizes a security framework using best practices in the SaaS industry with our key objectives centering on:
Netrivals values transparency when it comes to security and privacy to the extent that we can be without opening ourselves up to vulnerabilities. We are continuously improving the protections that have been implemented.
Data use: The data is strictly kept private and is not shared with third parties. Your data is only accessed by Netrivals’ technical and support teams in the case of a technical incident.
GDPR Compliant: Netrivals maintains compliance with the EU’s General Data Protection Regulation and maintains product features, corporate protocols, and legal documents to help our users and customers comply.